大鸟不久前看到Intel CPU的漏洞,真是恐怖啊,谷歌团队确实厉害,你看这么恐怕的漏洞都被找到了!
Google旗下的Project Zero团队发现了英特尔CPU存在两大严重漏洞:Spectre(幽灵)和Meltdown(熔断)。漏洞是因为先天性的架构设计缺陷所导致,可以让非特权用户访问系统内存从而读取敏感信息。换句话说,黑客可以通过这两个漏洞窃取计算机内的全部内存内容。
紧接着业界人士发现,受影响的不仅仅是英特尔,还有AMD和ARM。由于这三者在处理器市场上有着非常高的份额,意味着无论是Windows、Linux、Mac系统还是移动端的Android,都存在潜在的安全威胁,其中以英特尔芯片受影响最为严重。
当然大鸟说的不是这些,大鸟用的最多的是vps,大鸟已经看到,linode、vultr、阿里云已经着手开始修复了。
第一:我们看看linode的修复通知
大鸟登录到linode后台看到了,linode给出的消息。
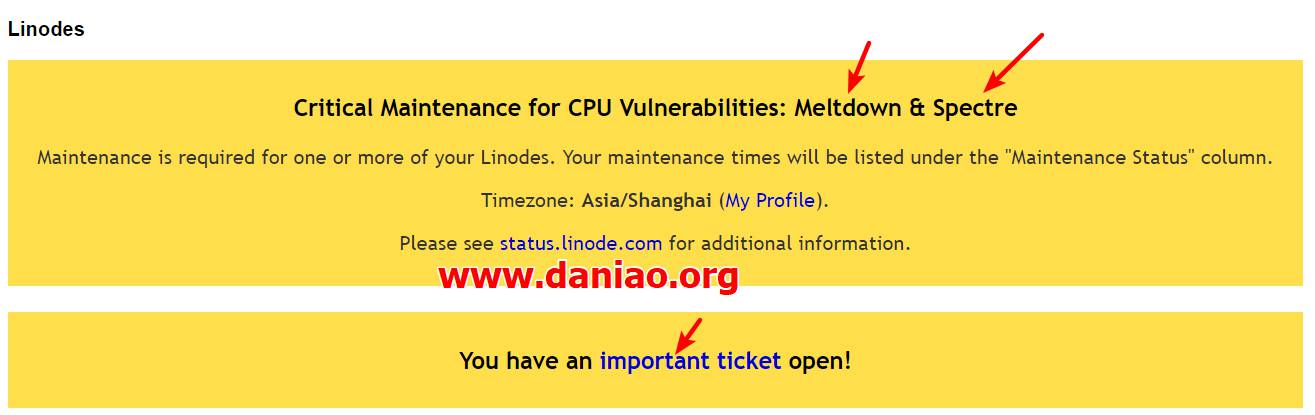
我看看看原文和翻译:
Critical Maintenance for CPU Vulnerabilities: Meltdown & Spectre
Maintenance is required for one or more of your Linodes. Your maintenance times will be listed under the “Maintenance Status” column.
Timezone: Asia/Shanghai (My Profile).
Please see status.linode.com for additional information.
CPU漏洞的重要维护:崩溃和幽灵
一个或多个Linode需要维护。您的维护时间将在“维护状态”栏中列出。
linode给我推送了一个很重要的通知,我们去看看。
全英文的通知,大鸟贴出来
Hello,
A number of serious security vulnerabilities affecting multiple CPU architectures were recently disclosed by Google’s Project Zero team as outlined in our blog post[1]. In order to address the disclosed vulnerabilities, the physical hardware on which your Linode resides will need to undergo maintenance. This is the first of several separate maintenances that will be necessary to fully mitigate these vulnerabilities. This maintenance specifically patches the Meltdown vulnerability; the Spectre vulnerability will be addressed in a future maintenance cycle. We will inform you of these maintenance cycles via additional tickets.
Scheduled maintenance windows are listed within the Linode Manager[2] in the time zone that was configured in your user’s My Profile[3]. The maintenance window of new Linodes and upgraded, migrated, or resized Linodes will be reflected in the Linode Manager[2], but you may not receive maintenance ticket updates for these changes.
The following Linode(s) have now been assigned a maintenance window in which a reboot will occur. Please note that these times can change as a result of the actions mentioned above. At this time your reboot schedule in UTC is as follows:
* 2018-01-15 7:30:00 PM UTC – linode5102565
You can prepare your Linode for this maintenance by following our Reboot Survival Guide. By following this guide before your maintenance, you will be able to ensure that services running on your Linode are resumed properly. The Reboot Survival Guide is available here:
https://www.linode.com/docs/uptime/reboot-survival-guide
These updates affect the underlying infrastructure that your Linode resides on and will not affect the data stored within your Linode. To further protect your Linode, we strongly recommend that you verify it is configured to boot using our latest kernel, which includes patches to help address these vulnerabilities. If your Linode’s Configuration Profile is set to utilize our latest kernel, your kernel will automatically be updated upon rebooting.
During the maintenance window, your Linode will be cleanly shut down and will be unavailable while we perform the updates. A two-hour window is allocated, however the actual downtime should be much less. After the maintenance has concluded, each Linode will be returned to its last state (running or powered off).
We regret the short notice and the downtime required for this maintenance. However, due to the severity of these vulnerabilities, we have no choice but to take swift and immediate action to ensure the safety and security of our customers. For these reasons, we must adhere to a strict timetable, and will not be able to reschedule or defer this maintenance.
If you experience any issues following the maintenance, please feel free to reach out to us and we will be happy to assist.
–Linode
翻译:
您好,
Google的Project Zero团队最近披露了一些影响多CPU架构的严重安全漏洞,如我们的博客文章[1]所述。为了解决所披露的漏洞,您的Linode所在的物理硬件将需要进行维护。这是完全缓解这些漏洞所必需的几个独立维护工作中的第一个。此维护专门修补了崩溃漏洞; 在未来的维护周期中,将会解决Specter漏洞。我们会通过额外的门票通知您这些维修周期。
计划维护窗口在用户的“我的配置文件”[3]中配置的时区中的Linode管理器[2]中列出。新Linode的维护窗口以及升级,迁移或调整大小的Linode将反映在Linode管理器[2]中,但您可能不会收到这些更改的维护工单更新。
现在已经为以下Linode分配了一个维护窗口,在该窗口中将会重新启动。请注意,由于上述行为,这些时间可能会改变。在这个时候你的UTC重启进度表如下:
* 2018-01-15 7:30:00 PM UTC – linode5102565
您可以按照我们的重新启动生存指南来准备您的Linode进行维护。在维护之前遵循本指南,您将能够确保在您的Linode上运行的服务能够正常恢复。“重新启动生存指南”位于以下位置:
https : //www.linode.com/docs/uptime/reboot-survival-guide
这些更新会影响您的Linode所驻留的基础架构,并且不会影响存储在您的Linode中的数据。为了进一步保护您的Linode,我们强烈建议您验证它是否配置为使用我们最新的内核进行引导,该内核包含可帮助解决这些漏洞的修补程序。如果你的Linode的配置文件被设置为使用我们最新的内核,你的内核将在重新启动后自动更新。
在维护期间,您的Linode将被彻底关闭,并在执行更新时不可用。分配一个两小时的窗口,但实际的停机时间应该少得多。维护结束后,每个Linode将返回到最后一个状态(运行或关闭)。
我们感到遗憾的是,这次维护所需的时间短暂和停机。但是,由于这些漏洞的严重性,我们别无选择,只能立即采取行动,确保客户的安全。由于这些原因,我们必须坚持严格的时间表,不能重新安排或延期维修。
如果您在维护之后遇到任何问题,请随时与我们联系,我们将很乐意提供帮助。
看的出来,linode还是第一时间开始了修复漏洞。我linode的技术团队点赞。
第二:我们看看vultr的通知
因为大鸟没有在vultr开机器,所以没有看到推送,只是在界面的最下面看到了一行通知!
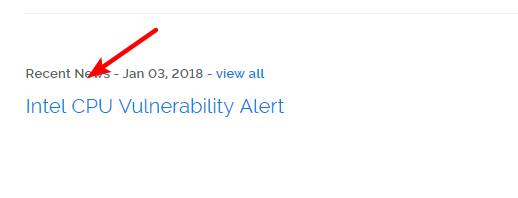
大鸟点进去看了下,发现有一个新闻的通知
Intel CPU Vulnerability Alert原文:
- Jan 03, 2018
As you may already be aware, a critical security flaw affecting Intel CPUs has been gaining traction in security research circles over the past several days.While the full details of the security issue are still restricted and there have been no official statements from Intel, our security team has been actively reviewing available information and planning for the necessary next steps. Our engineers have also been testing available kernel patches to ensure necessary upgrades proceed smoothly.
Current facts outline a vulnerability that likely affects a wide range of Intel processors. The patch to mitigate this issue will also likely require a one-time reboot of your instances. Once our team begins scheduling reboots, you will receive advance e-mail notification for any affected instances with a scheduled date and time. While reboots may cause a few minutes of downtime during the restart window, this will be a necessary step to ensure that your compute environment remains secure.
Note: This is an actively developing story and more details will become available in the coming days. Our team is actively monitoring this issue and we will update this article with any developments that directly impact your Vultr.com infrastructure.
Article Updates
– Intel has released a statement on the issue. A link can be found in the additional resources section below. Additionally, we are working closely with our Northeast Intel Representatives to gather additional information and resources directly from their Cloud Service Provider (CSP) team.
– The details of the security vulnerabilities have been disclosed early in CVE-2017-5753, CVE-2017-5715 and CVE-2017-5754. Our engineers have already applied updates to our infrastructure to ensure the security of our platform. The original date of the coordinated disclosure was scheduled for January 9th and information from hardware manufacturers is still currently incomplete. We are continuing to closely monitor the issue and will provide additional updates as necessary.
英特尔CPU漏洞警报译文:
- 2018年1月3日
正如你可能已经意识到的那样,安全研究界在过去的几天中,一个影响英特尔CPU的重要安全缺陷已经引起了人们的关注。虽然安全问题的全部细节仍然受到限制,英特尔也没有正式声明,但我们的安全团队一直在积极审查可用的信息,并计划采取必要的下一步措施。我们的工程师也一直在测试可用的内核补丁,以确保必要的升级顺利进行。
目前的事实勾勒出一个可能影响到大量英特尔处理器的漏洞。缓解此问题的修补程序也可能需要一次性重新启动您的实例。一旦我们的团队开始安排重新启动,您将收到事先预定的日期和时间受影响的实例的电子邮件通知。虽然重新启动可能会在重新启动窗口中导致几分钟的停机时间,但这将是确保计算环境保持安全的必要步骤。
注:这是一个积极发展的故事,在未来的日子里将有更多的细节。我们的团队正在积极监控这个问题,我们将更新这篇文章,直接影响您的Vultr.com基础设施的任何发展。
文章更新
– 英特尔已经发布了关于这个问题的声明。链接可以在下面的附加资源部分找到。此外,我们还与东北英特尔代表密切合作,直接从其云服务提供商(CSP)团队收集更多信息和资源。
– CVE-2017-5753,CVE-2017-5715和CVE-2017-5754中详细披露了安全漏洞的详细信息。我们的工程师已经将更新应用于我们的基础架构,以确保我们平台的安全。协调披露的原始日期定于1月9日,硬件制造商的信息仍然不完整。我们正在继续密切关注这个问题,并会根据需要提供更多更新。